Welcome to Day 2 of Pwn2Own Vancouver 2023! We’ll be updating this blog in real time as results become available. We’re excited to say that all unique winning entries will receive the full payout during this year’s contest. We’ll update this blog throughout the day with results as they come in.
SUCCESS / COLLISION - Thomas Imbert (@masthoon) and Thomas Bouzerar (@MajorTomSec) from Synacktiv (@Synacktiv) demonstrated a 3-bug chain against Oracle VirtualBox with a Host EoP. One bug was previously known. They still earn $80,000 and 8 Master of Pwn points.
SUCCESS - @hoangnx99, @rskvp93, and @_q5ca from Team Viettel (@vcslab) used a 2-bug chain in their attempt against Microsoft Teams. They earn $75,000 and 8 Master of Pwn points.
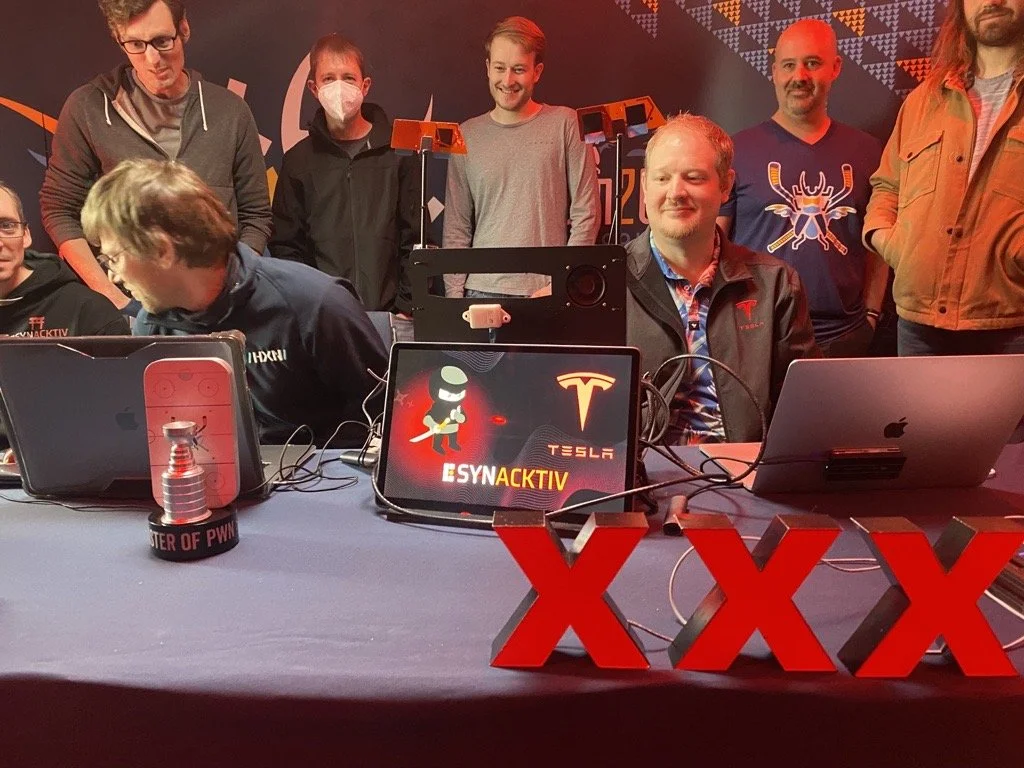
SUCCESS - David Berard (@_p0ly_) and Vincent Dehors (@vdehors) from Synacktiv (@Synacktiv) used a heap overflow and an OOB write to exploit Tesla - Infotainment Unconfined Root. They qualify for a Tier 2 award, earning $250,000 and 25 Master of Pwn points.
SUCCESS - Tanguy Dubroca (@SidewayRE) from Synacktiv (@Synacktiv) used an incorrect pointer scaling leading to privilege escalation on Ubuntu Desktop. They earn $30,000 and 3 Master of Pwn points.
That wraps up Day 2 of Pwn2Own Vancouver 2023! We awarded $475,000 for 10 unique zero-days during the second day of the contest. We’ll continue posting results and videos to Twitter, YouTube, Mastodon, LinkedIn, and Instagram, so follow us on your favorite flavor of social media for the latest news from the event.